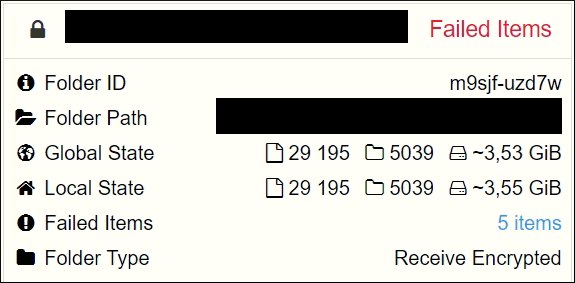
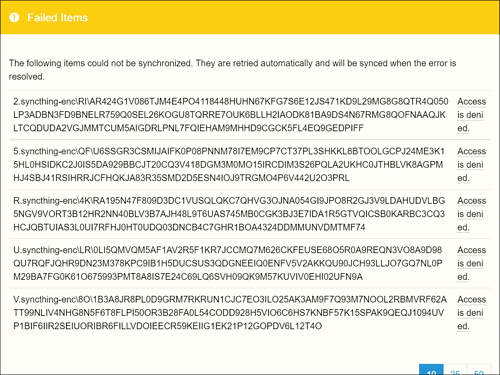
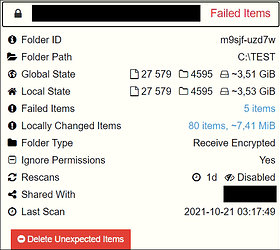
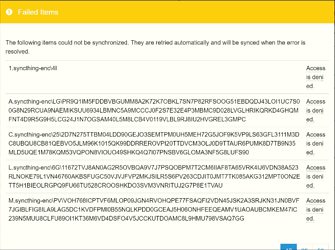
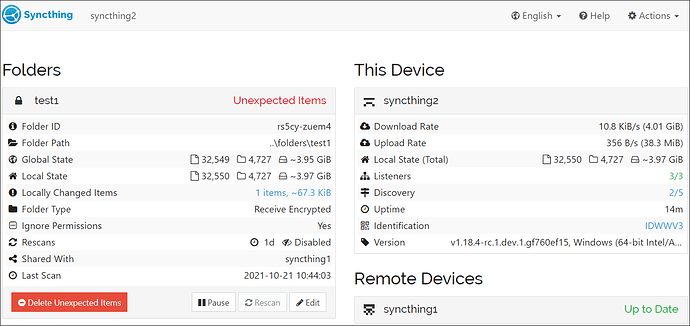
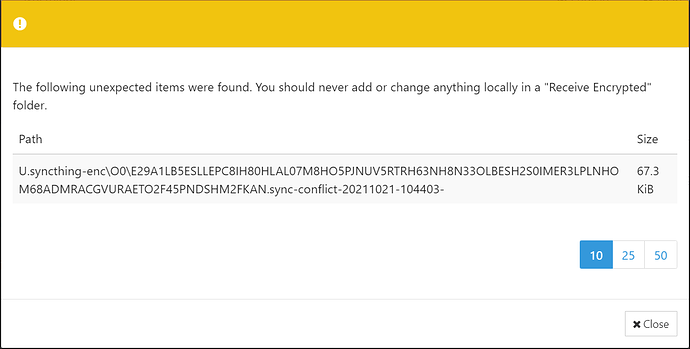
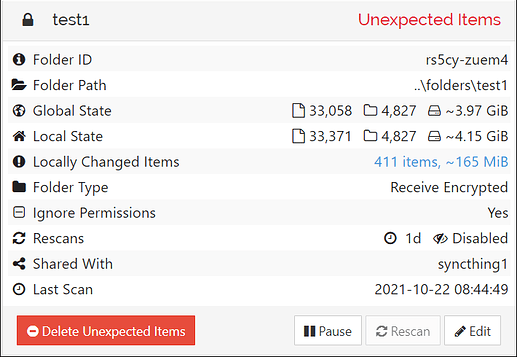
The problem isn’t ignore patterns, it’s that the modification time of the file on the receive-encrypted device gets updated. That results in an unexpected item. A subsequent change on the remote creates a conflict between that unexpected local change and the correct remote change. Syncthing then creates the conflict file when syncing. You can identify the sequence by the Length and the 0x8 local flag (locally changed).
[IDWWV] 2021/10/21 10:42:42.397749 lowlevel.go:264: DEBUG: insert (local); folde
r="rs5cy-zuem4" File{Name:"U.syncthing-enc/O0/E29A1LB5ESLLEPC8IH80HLAL07M8HO5PJN
UV5RTRH63NH8N33OLBESH2S0IMER3LPLNHOM68ADMRACGVURAETO2F45PNDSHM2FKAN", Sequence:3
7269, Permissions:0644, ModTime:2009-02-14 08:31:30 +0900 KST, Version:{[{AAAAAA
A 1634780429}]}, VersionHash:, Length:68942, Deleted:false, Invalid:false, Local
Flags:0x0, NoPermissions:false, BlockSize:131112, Blocks:[Block{0/68455/0/d468ad
f0f04e538fc0b21be70747a655616428ada18910cb1b03180dc49a2517cef42f5394884b73c62209
3dcaaccdef}], BlocksHash:8828a15e26e01655ee42ad69b663f5ba11571f623b0b17187dcd8d3
f6710f8d3}
[...]
[IDWWV] 2021/10/21 10:44:03.145378 lowlevel.go:264: DEBUG: insert (local); folder="rs5cy-zuem4" File{Name:"U.syncthing-enc/O0/E29A1LB5ESLLEPC8IH80HLAL07M8HO5PJNUV5RTRH63NH8N33OLBESH2S0IMER3LPLNHOM68ADMRACGVURAETO2F45PNDSHM2FKAN", Sequence:37303, Permissions:0644, ModTime:2021-10-21 10:42:40.5978892 +0900 KST, Version:{[{AAAAAAA 1634780429} {IDWWV34 1634780643}]}, VersionHash:, Length:68942, Deleted:false, Invalid:false, LocalFlags:0x8, NoPermissions:true, BlockSize:131112, Blocks:[], BlocksHash:}
[...]
[IDWWV] 2021/10/21 10:44:03.299408 lowlevel.go:264: DEBUG: insert (local); folder="rs5cy-zuem4" File{Name:"U.syncthing-enc/O0/E29A1LB5ESLLEPC8IH80HLAL07M8HO5PJNUV5RTRH63NH8N33OLBESH2S0IMER3LPLNHOM68ADMRACGVURAETO2F45PNDSHM2FKAN", Sequence:37304, Permissions:0644, ModTime:2009-02-14 08:31:30 +0900 KST, Version:{[{AAAAAAA 1634780638}]}, VersionHash:, Length:68956, Deleted:false, Invalid:false, LocalFlags:0x0, NoPermissions:false, BlockSize:131112, Blocks:[Block{0/68469/0/e6bd0d9ee00b4b3b71edb0adc734d93ae9e08da8f8b98d88decd6d7a53b8343977d7636daf6d89a8b0f2595fbbc81572}], BlocksHash:05039d85df7e1776ba1d18fc80021c9f3920fcfec007b944e590312bf6b44a36}
[...]
[IDWWV] 2021/10/21 10:44:03.730495 lowlevel.go:264: DEBUG: insert (local); folder="rs5cy-zuem4" File{Name:"U.syncthing-enc/O0/E29A1LB5ESLLEPC8IH80HLAL07M8HO5PJNUV5RTRH63NH8N33OLBESH2S0IMER3LPLNHOM68ADMRACGVURAETO2F45PNDSHM2FKAN.sync-conflict-20211021-104403-", Sequence:37305, Permissions:0644, ModTime:2021-10-21 10:42:40.5978892 +0900 KST, Version:{[{IDWWV34 1634780643}]}, VersionHash:, Length:68942, Deleted:false, Invalid:false, LocalFlags:0x8, NoPermissions:true, BlockSize:131072, Blocks:[], BlocksHash:}
This in principle is all correct, just that the conflict on an encrypted device isn’t very helpful. However we also don’t want to remove that file automatically, for the usual reasons (Syncthing should never delete any data automatically). I don’t have a good idea how to better handle this scenario right now and the current behaviour is safe and can be resolved, even though it’s admittedly not obvious what happens.
 .
. .
. . I’ve cherry-picked the commit and I’m testing everything right now. There’s been no local additions so far.
. I’ve cherry-picked the commit and I’m testing everything right now. There’s been no local additions so far.