Hello, I’m tying to use my own discovery server with docker and lets encrypt.
So, I followed this article
I setting up https and reverse proxy.
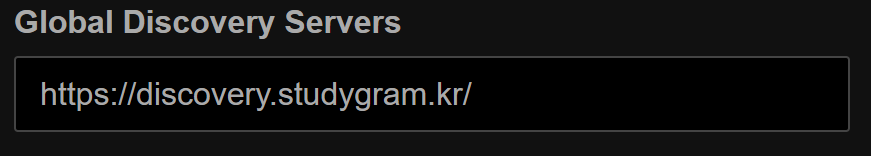
So, I enter my server name to syncthing’s Global discovery servers
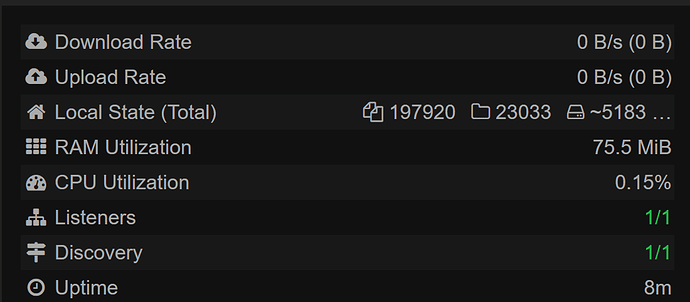
But I cannot connect to discovery server.
I got log global.go:229: DEBUG: announce POST: 404 Not Found
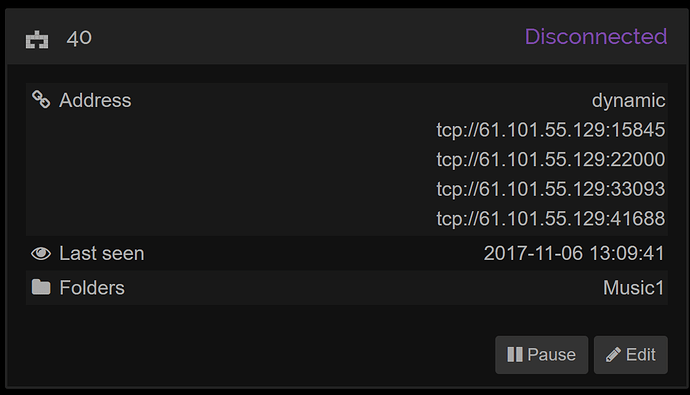
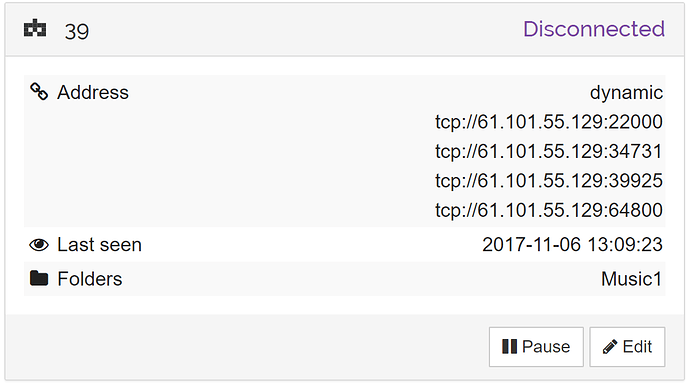
First I thought that reverse proxy is not working. But when I send some http requests to dicovery server directly, I get same response.
And discovery server’s log is below
stdiscosrv v0.14.40-rc.4+21-g0ee1146 (go1.9.2 linux-amd64) teamcity@build.syncthing.net 2017-11-07 07:25:05 UTC
Stats: 0.00 announces/s, 0.00 queries/s, 0.00 answers/s, 0.00 errors/s
Stats: 0.00 announces/s, 0.00 queries/s, 0.00 answers/s, 0.00 errors/s
Stats: 0.00 announces/s, 0.00 queries/s, 0.00 answers/s, 0.00 errors/s
Stats: 0.00 announces/s, 0.00 queries/s, 0.00 answers/s, 0.00 errors/s
Stats: 0.00 announces/s, 0.00 queries/s, 0.00 answers/s, 0.00 errors/s
Database: 0 devices, 0 addresses
Stats: 0.00 announces/s, 0.00 queries/s, 0.00 answers/s, 0.00 errors/s
There’s any announces even error (like handshake)
Below is my nginx setting
# If we receive X-Forwarded-Proto, pass it through; otherwise, pass along the
# scheme used to connect to this server
map $http_x_forwarded_proto $proxy_x_forwarded_proto {
default $http_x_forwarded_proto;
'' $scheme;
}
# If we receive X-Forwarded-Port, pass it through; otherwise, pass along the
# server port the client connected to
map $http_x_forwarded_port $proxy_x_forwarded_port {
default $http_x_forwarded_port;
'' $server_port;
}
# If we receive Upgrade, set Connection to "upgrade"; otherwise, delete any
# Connection header that may have been passed to this server
map $http_upgrade $proxy_connection {
default upgrade;
'' close;
}
# Apply fix for very long server names
server_names_hash_bucket_size 128;
# Default dhparam
# Set appropriate X-Forwarded-Ssl header
map $scheme $proxy_x_forwarded_ssl {
default off;
https on;
}
gzip_types text/plain text/css application/javascript application/json application/x-javascript text/xml application/xml application/xml+rss text/javascript;
log_format vhost '$host $remote_addr - $remote_user [$time_local] '
'"$request" $status $body_bytes_sent '
'"$http_referer" "$http_user_agent"';
access_log off;
# HTTP 1.1 support
proxy_http_version 1.1;
proxy_buffering off;
proxy_set_header Host $http_host;
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection $proxy_connection;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $proxy_x_forwarded_proto;
proxy_set_header X-Forwarded-Ssl $proxy_x_forwarded_ssl;
proxy_set_header X-Forwarded-Port $proxy_x_forwarded_port;
proxy_set_header X-SSL-Cert $ssl_client_cert;
# Mitigate httpoxy attack (see README for details)
proxy_set_header Proxy "";
server {
server_name _; # This is just an invalid value which will never trigger on a real hostname.
listen 80;
access_log /var/log/nginx/access.log vhost;
return 503;
}
# discovery.studygram.kr
upstream discovery.studygram.kr {
## Can be connect with "sdd_default" network
# syncthing_discovery_run
server 172.19.0.2:8443;
}
server {
server_name discovery.studygram.kr;
listen 80 ;
access_log /var/log/nginx/access.log vhost;
return 301 https://$host$request_uri;
}
server {
server_name discovery.studygram.kr;
listen 443 ssl http2 ;
access_log /var/log/nginx/access.log vhost;
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
ssl_ciphers 'ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA:ECDHE-RSA-AES256-SHA:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:DHE-RSA-AES256-SHA256:DHE-RSA-AES256-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-SHA256:AES256-SHA256:AES128-SHA:AES256-SHA:!DSS';
ssl_prefer_server_ciphers on;
ssl_session_timeout 5m;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_certificate /etc/nginx/certs/discovery.studygram.kr.crt;
ssl_certificate_key /etc/nginx/certs/discovery.studygram.kr.key;
ssl_trusted_certificate /etc/nginx/certs/discovery.studygram.kr.chain.pem;
ssl_dhparam /etc/nginx/certs/discovery.studygram.kr.dhparam.pem;
add_header Strict-Transport-Security "max-age=31536000";
ssl_verify_client optional_no_ca;
add_header Strict-Transport-Security "max-age=31536000";
include /etc/nginx/vhost.d/default;
location / {
proxy_pass http://discovery.studygram.kr/;
}
}
Thank you in abvance